1990
Endogenous Technological Change
Paul Romer publishes his seminal paper establishing the economic theory that would
justify the information economy. Ideas, unlike physical goods, can be shared without
being depleted—creating the theoretical foundation for infinite growth through
knowledge sharing.
August 1991
World Wide Web Goes Public
Tim Berners-Lee releases the first web browser and server software on the internet.
The web's open architecture—built on HTTP, HTML, and URL standards—embodies the
decentralized, non-proprietary ethos that would define the era.
1992
The End of History
Francis Fukuyama's book declares liberal democracy victorious. The ideological
battles of the 20th century are over; free markets and democratic governance
represent humanity's endpoint. Technology becomes a vehicle for this inevitable
historical trajectory.
April 1993
The Clipper Chip Proposal
The Clinton administration proposes the Clipper Chip—a hardware encryption standard
with government backdoor access. The proposal reveals the first major tension:
openness versus surveillance in the digital realm.
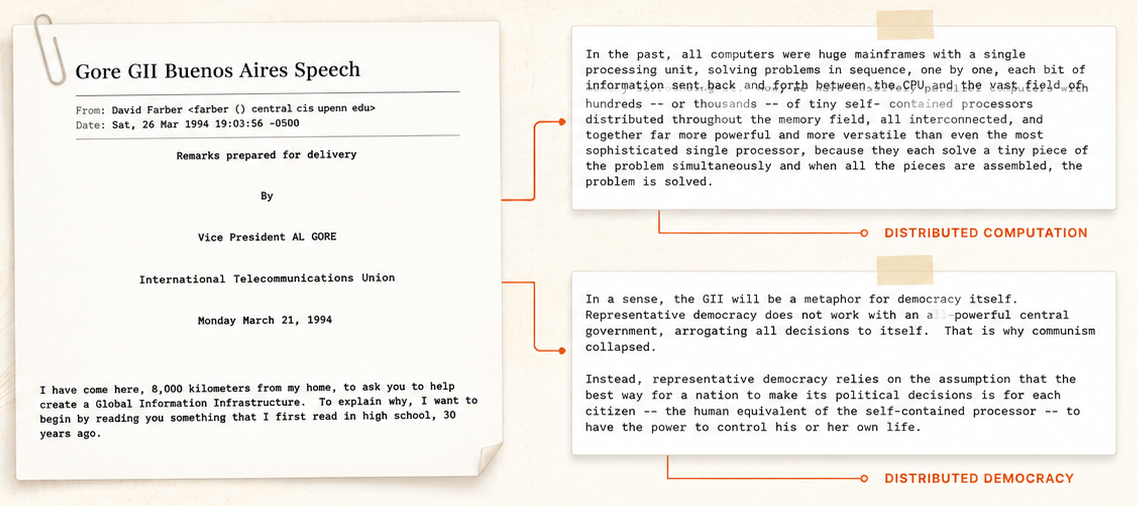
March 21, 1994
Al Gore's Buenos Aires Speech
Vice President Gore announces the Global Information Infrastructure (GII) initiative,
outlining five principles that would guide U.S. digital policy: private sector leadership,
competition, open access, universal service, and flexible regulation.
May 1994
Matt Blaze's Discovery
AT&T researcher Matt Blaze discovers a critical vulnerability in the Clipper Chip's
escrow system. The technical failure accelerates the shift from hardware-based
surveillance to market-based dominance strategies.
February 8, 1996
Barlow's Declaration
John Perry Barlow publishes "A Declaration of the Independence of Cyberspace" in Davos,
proclaiming: "Governments of the Industrial World, you weary giants of flesh and steel,
I come from Cyberspace, the new home of Mind."
February 1996
Telecommunications Act
The most significant overhaul of U.S. communications law in 62 years. Title I vs Title II
classification debates begin. Section 230 is inserted—"the 26 words that created the Internet"—
providing liability protection for online platforms.
February 1997
WTO Basic Telecom Agreement
69 countries commit to opening their telecommunications markets to foreign competition.
The agreement institutionalizes the liberal approach to digital infrastructure globally,
embedding market principles in international trade law.
1998
ICANN Formation
The Internet Corporation for Assigned Names and Numbers is created to manage domain names
and IP addresses. The U.S. government retains ultimate authority, establishing a model
of private governance with public oversight.
March 2000
Clinton's Trojan Horse
President Clinton admits the difficulty of regulating the internet: "Good luck! That's
sort of like trying to nail Jello to the wall." The comment reveals both the hubris of the hegemon and a
fundamental category error—treating the internet as merely "information" rather than
infrastructure.